by FastNetMon | Oct 8, 2025 | Blog
Guest post by Vincentas Grinius, Co-Founder at IPXO The shift to IPv6 has escalated into a matter of national security, as nations lagging in adoption are increasingly exposed to cyber threats and diminished control over their digital infrastructure due to the limited...
by FastNetMon | Oct 8, 2025 | Blog
Incident summary: Date: October 6, 2025 Targets: Steam, Riot Games, PlayStation Network, AWS, and others Peak bandwidth (unconfirmed): 29.69 Tbps Suspected source: Aisuru botnet Attack vector (reported): TCP-based carpet bomb traffic Status: Under investigation — no...
by FastNetMon | Oct 1, 2025 | Blog
ShadowV2 has been identified as a new DDoS-as-a-service platform that stands out for its use of cloud infrastructure. Instead of relying on home routers or compromised IoT devices, it exploits misconfigured Docker daemons running in public cloud environments. Many of...
by FastNetMon | Sep 24, 2025 | Blog
When we talk about DDoS attacks, the focus is almost always on protecting services from inbound floods. But there’s another side to the story that often goes unnoticed: outbound DDoS attacks. These are attacks where malicious traffic originates from inside your...
by FastNetMon | Sep 23, 2025 | Blog
The cybersecurity landscape witnessed a new benchmark in DDoS attacks as Cloudflare reported mitigating a hyper-volumetric assault that peaked at 22.2 terabits per second (Tbps) and 10.6 billion packets per second (Bpps). This attack more than doubled the previous UDP...
by FastNetMon | Sep 23, 2025 | Blog
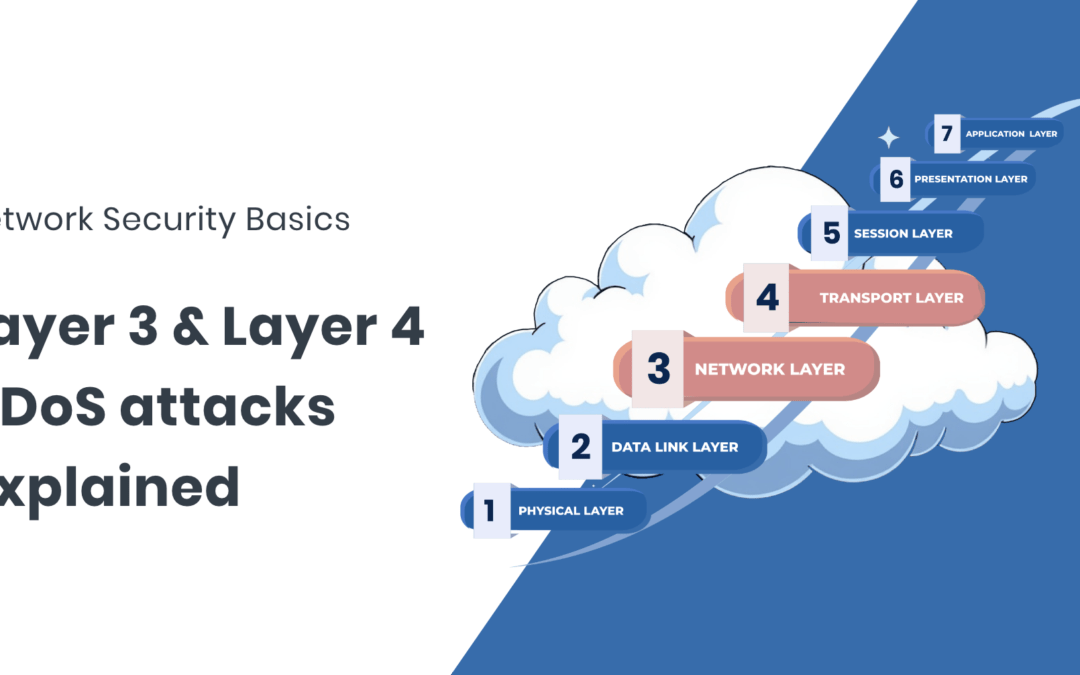
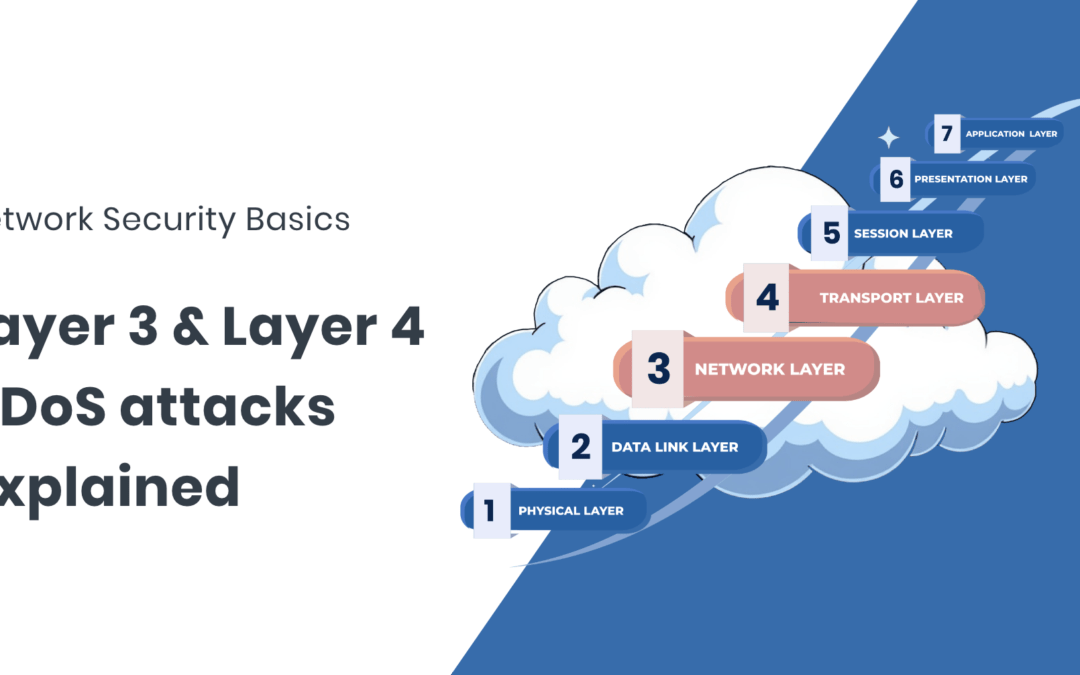
What L3 and L4 DDoS attacks are, how they work, and what defenders need to know DDoS attacks at Layers 3 and 4 (the Network and Transport layers) are some of the most common and disruptive seen on the public internet. While often lumped together, they behave...