by FastNetMon | Oct 16, 2025 | Blog
Every now and then, a network operator’s inbox lights up with a DDoS ransom note — bold claims, big threats, and a bitcoin address waiting for payment. We’ve seen plenty of them ourselves. Some come from actors with real bandwidth behind them; others are clearly...
by FastNetMon | Sep 23, 2025 | Blog
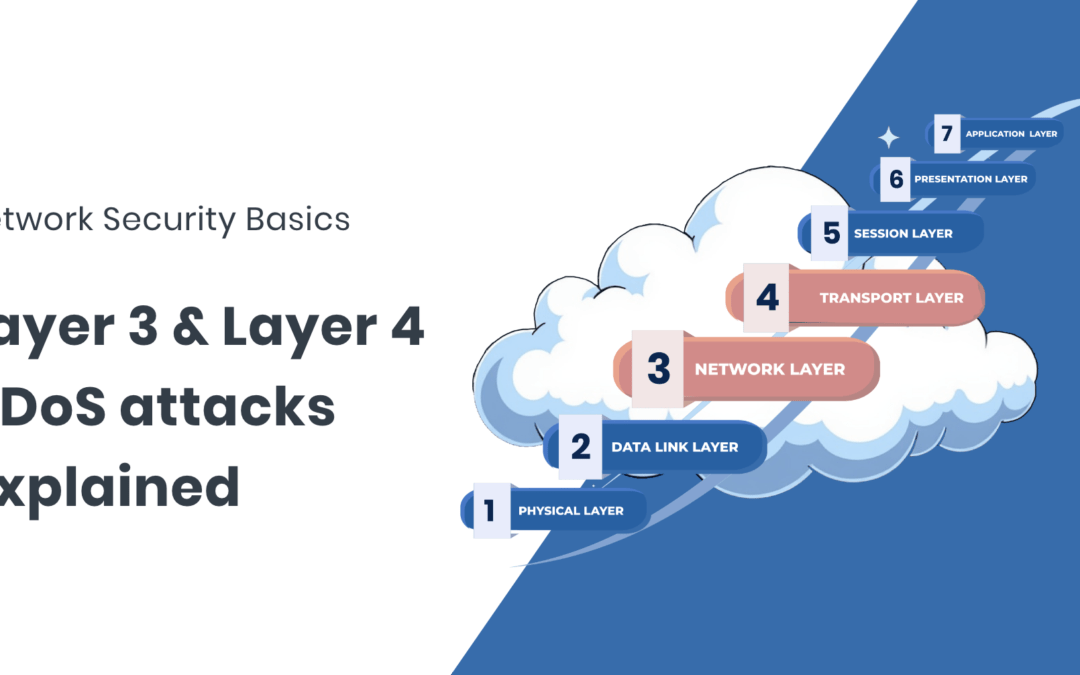
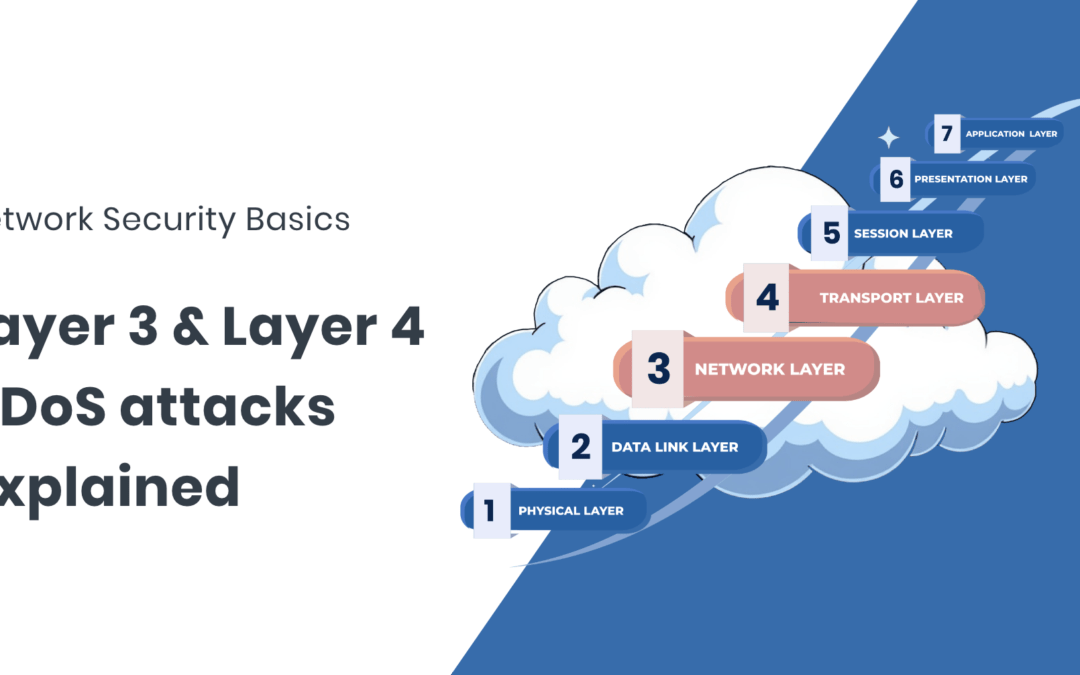
What L3 and L4 DDoS attacks are, how they work, and what defenders need to know DDoS attacks at Layers 3 and 4 (the Network and Transport layers) are some of the most common and disruptive seen on the public internet. While often lumped together, they behave...
by FastNetMon | Sep 16, 2025 | Blog
DDoS attacks remain one of the most disruptive threats facing ISPs, backbone networks, hosting providers, and enterprises. Detecting the attacks quickly is essential to keeping networks stable and services running. This guide looks at how network engineers can...
by FastNetMon | Sep 10, 2025 | Blog
Despite being a decades-old threat, DDoS attacks still come with a cloud of misunderstanding. Every time a myth goes unchecked, organisations risk underestimating threats or misallocating resources. This post debunks the most stubborn DDoS myths and explains what...
by FastNetMon | Sep 3, 2025 | Blog
Introduction: Questions you always wanted to ask about DDoS DDoS is one of those topics that everyone in the industry has heard about, but few feel confident they fully understand. Maybe you’ve sat in a meeting where terms like “RTBH,” “FlowSpec,” or “amplification”...