by FastNetMon | Sep 4, 2025 | FastNetMon Blog
Application-layer and “low-and-slow” DDoS attacks explained by DDoS defence professionals Application-layer (L7) and “low-and-slow” DDoS attacks are among the most insidious forms of denial-of-service threats. Rather than saturating bandwidth, they burn server CPU,...
by FastNetMon | Aug 12, 2025 | FastNetMon Blog
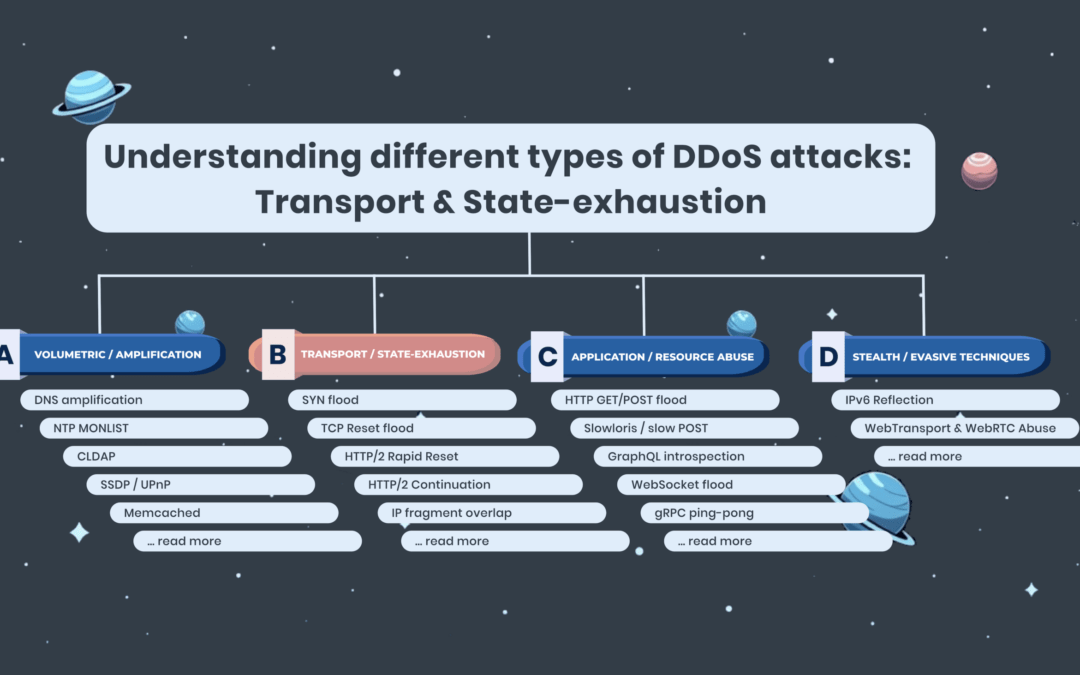
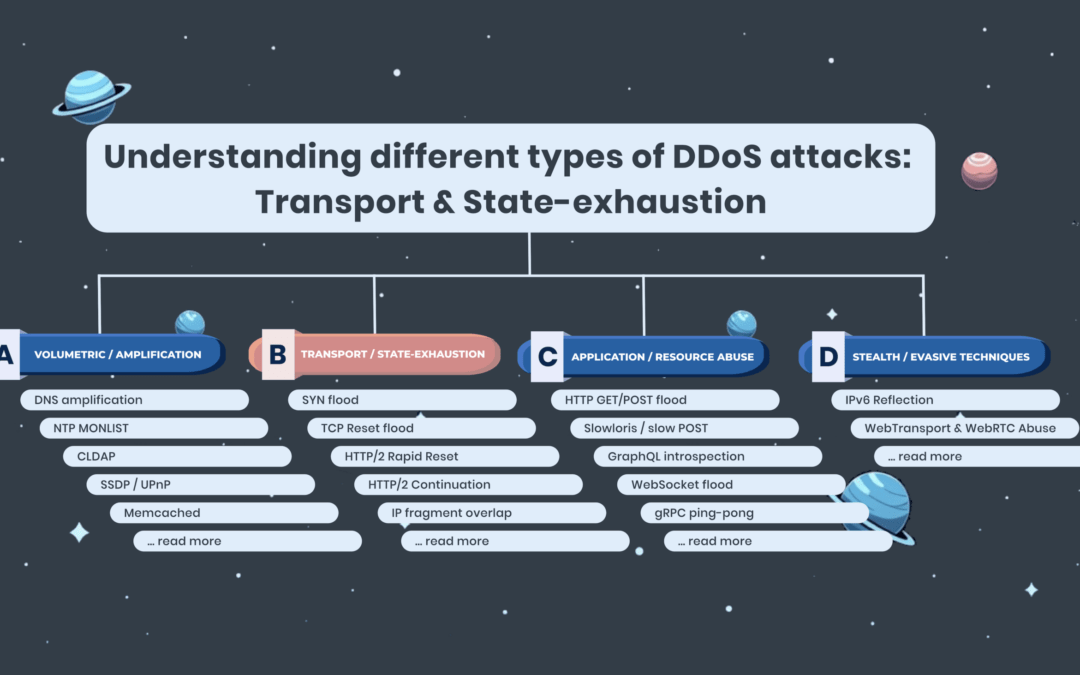
How connection state exhaustion attacks threaten your firewalls and proxies Transport and state-exhaustion DDoS attacks represent a growing and sophisticated category of denial-of-service threats targeting the resource limitations of network infrastructure. Instead of...
by FastNetMon | Jul 30, 2025 | FastNetMon Blog
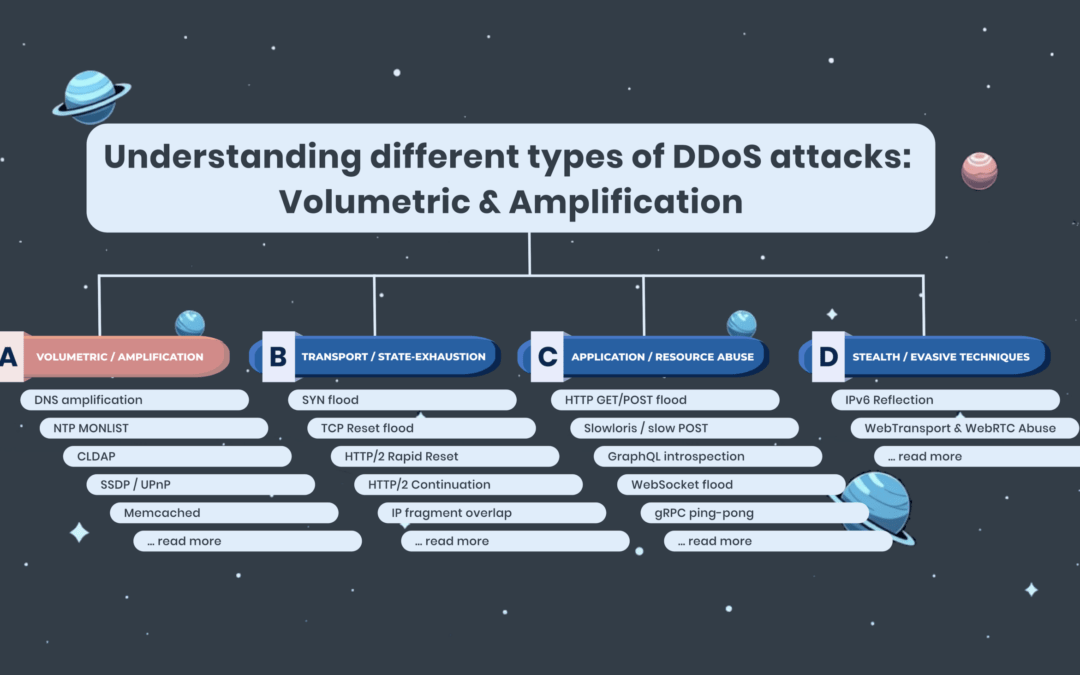
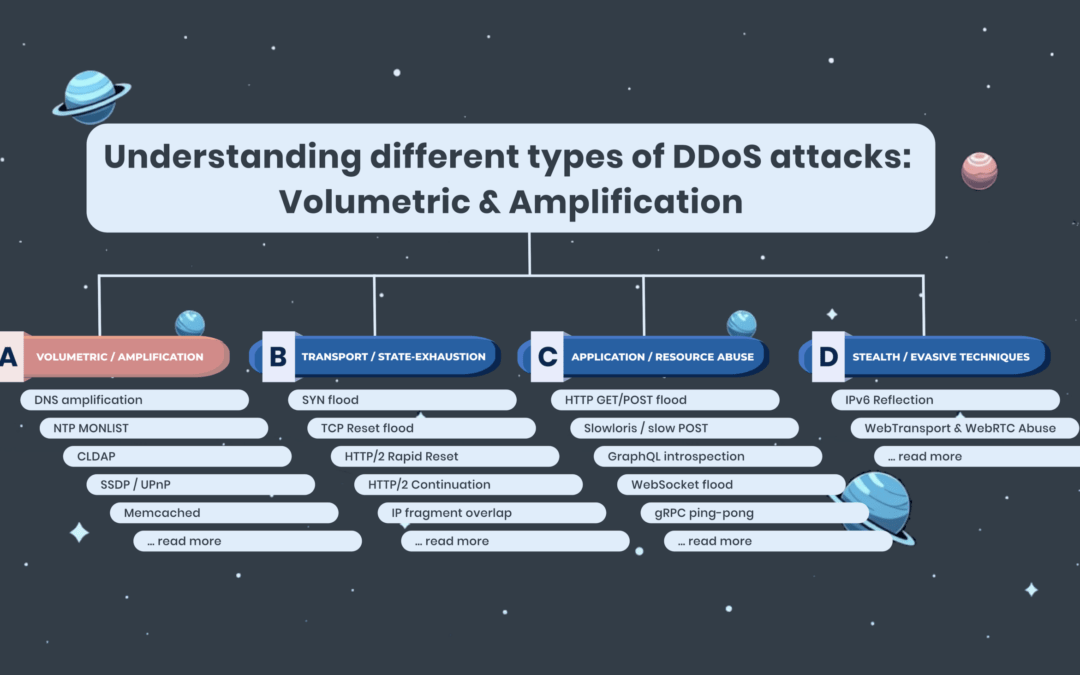
How bandwidth-focused DDoS campaigns work—and why they’re still effective at scale Volumetric DDoS attacks remain one of the most common and disruptive forms of denial-of-service activity across the internet. Despite evolving tactics, the core objective is the same:...
by FastNetMon | Jul 25, 2025 | FastNetMon Blog
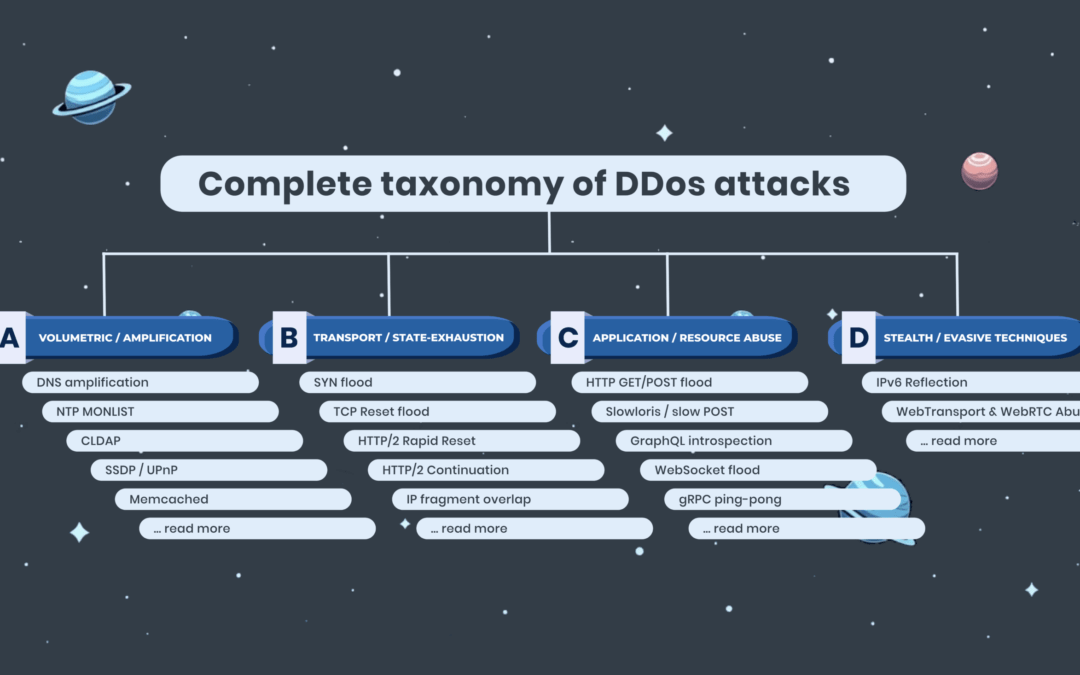
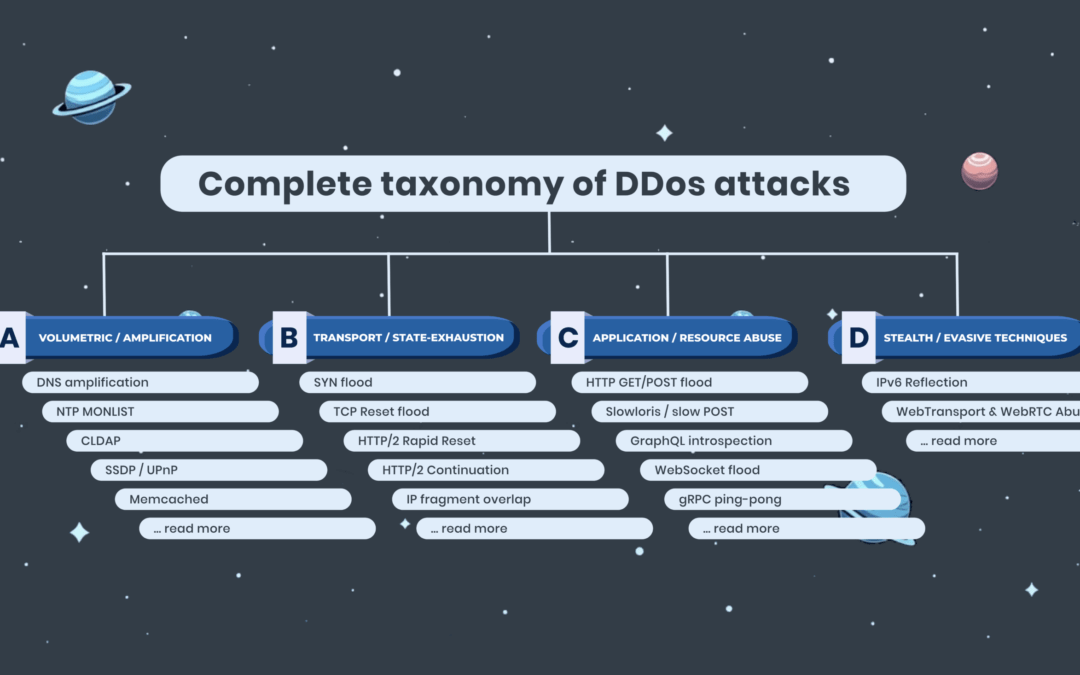
A practical breakdown of DDoS attack vectors, built for network operators When your NOC wallboard lights up red, you don’t have 5 seconds. And if you’re relying on manual triage at that point, it is a tough job. Ideally, you’ve preloaded mitigation rules for the most...