Introduction
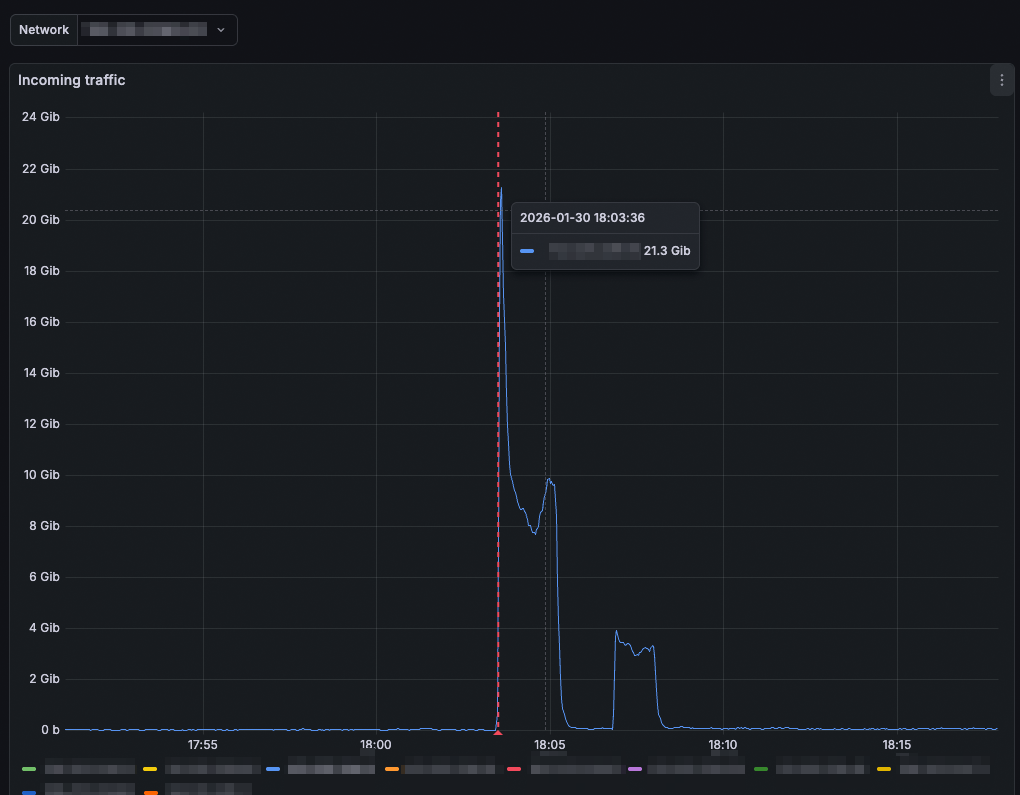
For network engineers running ISP infrastructure, DDoS activity does not always present as an obvious incident. Instead, unusual traffic patterns may only become visible during later analysis, long after the event itself.
This was the operational reality at Australian ISP Pentanet. As the network grew and traffic arrived through multiple upstream and peering paths, existing monitoring tools provided visibility into traffic trends but lacked real-time detection and automated response.
At the same time, customers increasingly expected DDoS protection as part of connectivity services. Pentanet needed a way to gain immediate visibility into edge traffic while introducing scalable DDoS detection and mitigation capabilities into their network.
This case study is based on discussions with Jeremy Hall, CTO and Head of Product at Pentanet, about Pentanet’s deployment and operational use of FastNetMon. We appreciate him for taking the time to share his team’s experience.
About the Customer
Pentanet is an Australian telecommunications provider delivering connectivity services to residential and enterprise customers across Australia. In addition to traditional ISP services, Pentanet also exclusively hosts and operates the CloudGG platform, delivering NVIDIA GeForce NOW cloud gaming services across Australia and New Zealand as an official NVIDIA alliance partner.
This combination of broadband access and latency-sensitive cloud infrastructure creates a diverse and demanding traffic environment. Pentanet’s network supports multiple service types simultaneously, including:
- carrier-grade NAT (CGN) networks
- residential services with public IPs
- enterprise customer connectivity
- internal infrastructure systems supporting hosted platforms such as CloudGG
Traffic reaches the network through multiple paths, including transit providers, internet exchanges, and peered cloud networks. Each ingress path introduces different traffic characteristics, operational requirements, and potential attack vectors.
For an ISP operating both consumer connectivity and real-time cloud platforms, maintaining consistent service quality depends on understanding traffic behaviour at the edge — where congestion, abuse, and DDoS activity first become visible.
The Challenge: Sample-based flow monitoring was not enough
Before deploying FastNetMon, Pentanet relied on a sample-based flow monitoring solution. While useful for general monitoring, it lacked the granularity required for operational security. At the same time, customers increasingly expected DDoS protection as part of connectivity services, creating a need for detection and mitigation capabilities that could operate directly within Pentanet’s own network.
"We had challenges with limited visibility coming from a lack of granularity… making post-incident analysis difficult, with no clear pathway to alerts or real-time automated actions"
The team could observe overall traffic trends, but the monitoring setup did not reliably detect attacks in real time. Incidents were typically identified only after investigation, by manually correlating spikes in throughput graphs with unusual traffic behaviour. In practice, detection depended on engineers recognising anomalies themselves rather than the network generating actionable alerts.
Limits of Upstream Mitigation
Pentanet also had access to automated mitigation from an upstream provider. However, this approach introduced operational gaps:
- mitigation activated slowly
- visibility into attack behaviour was limited
- less effective against highly distributed attacks
Large distributed attacks increasingly arrived through internet exchanges, peered cloud providers, or alternative transit connections, bypassing upstream controls.
The team needed detection capability within their own network — close to the edge routers handling incoming traffic.
Implementation: Introducing FastNetMon
Pentanet deployed FastNetMon initially as a proof of concept focused on detection and alerting. The results appeared quickly: Just days after deploying a trial PoC it was detecting actual DDoS which otherwise would have gone unnoticed.
Real-Time Edge Visibility with sFlow
FastNetMon receives sFlow telemetry from Pentanet’s edge routers and continuously analyses traffic in real time.
“FastNetMon receives sFlow from each of our edge routers and gives us high resolution insight into the traffic on our edge.”
This provides engineers with immediate visibility into host-level traffic behaviour rather than aggregated historical metrics. Traffic anomalies become operational events instead of forensic discoveries.
Detection Built Around Network Structure
Pentanet configured FastNetMon to reflect how their network actually operates.
Separate host groups are defined for:
- CGN IP ranges
- residential services with public IPs
- enterprise customers
- Pentanet’s internal infrastructure
Each group uses independent detection thresholds and mitigation actions. This prevents enterprise traffic patterns from triggering residential thresholds and allows policies aligned with real traffic expectations.
Initial thresholds are based on Mbps and packets-per-second values appropriate to each customer class. FastNetMon’s built-in baselining tool helps establish these safely:
"FastNetMon’s built-in baselining tool is super useful and made defining our first set of thresholds easy and low risk."
The team now iterates toward more adaptive detection using the flexible_thresholds feature.
Automated Mitigation via BGP RTBH
FastNetMon integrates directly with Pentanet’s routing infrastructure to automate mitigation.
The deployment includes:
- GoBGP peering from FastNetMon
- integration with Arista EOS routers
- automated Remote Triggered Black Hole (RTBH) announcements
When traffic exceeds defined thresholds, FastNetMon automatically triggers mitigation through BGP signalling, suppressing attack traffic without manual intervention.
Detection and response occur as part of normal routing behaviour rather than a separate workflow.
Operational Integration
FastNetMon integrates into existing operational tooling instead of introducing new processes.
Notifications are sent to Slack for visibility, while incident response workflows are integrated with PagerDuty using FastNetMon’s email notification system.
“Ban events from FastNetMon create a PagerDuty incident and unban events resolve a correlated incident.”
This links detection directly to the incident lifecycle: alerts generate incidents automatically, and mitigation resolution closes them.
Outcomes and Operational Impact
Following deployment, DDoS events that previously went unnoticed are now detected and surfaced in near real time. FastNetMon quickly begins identifying active attacks during the proof-of-concept phase, providing immediate operational value.
Pentanet gained:
- near real-time DDoS detection at the network edge
- automated response through BGP RTBH mitigation
- immediate operational alerting via Slack and PagerDuty
- improved visibility into traffic behaviour across customer groups
Detection and mitigation now operate as part of normal network workflows rather than manual investigation. Events generated by FastNetMon automatically create and resolve incidents in PagerDuty, allowing engineers to monitor the situation in real-time while reducing manual and investigative overhead.
Beyond DDoS protection, FastNetMon also provides high-resolution traffic visibility, helping the team better understand baseline behaviour across different customer segments.
Why FastNetMon Fits the Environment
For Pentanet, adopting FastNetMon is less about introducing a new platform and more about extending existing network operations with tooling that behaves the way engineers expect.
The system integrates naturally into a network-centric workflow. Its network-device-style CLI, straightforward configuration model, and clear documentation allow the team to deploy and operate it without adding operational complexity. Configuration remains simple while still providing the flexibility needed to support different customer types and traffic profiles across the network.
Equally important is predictability. Detection, alerting, and mitigation behave consistently, allowing FastNetMon to become part of daily operations rather than a tool used only during incidents.
“The product simply does what it’s supposed to do.”
In practice, that reliability — combined with fast detection and seamless integration into existing tooling — is what makes FastNetMon a practical fit for Pentanet’s production environment.