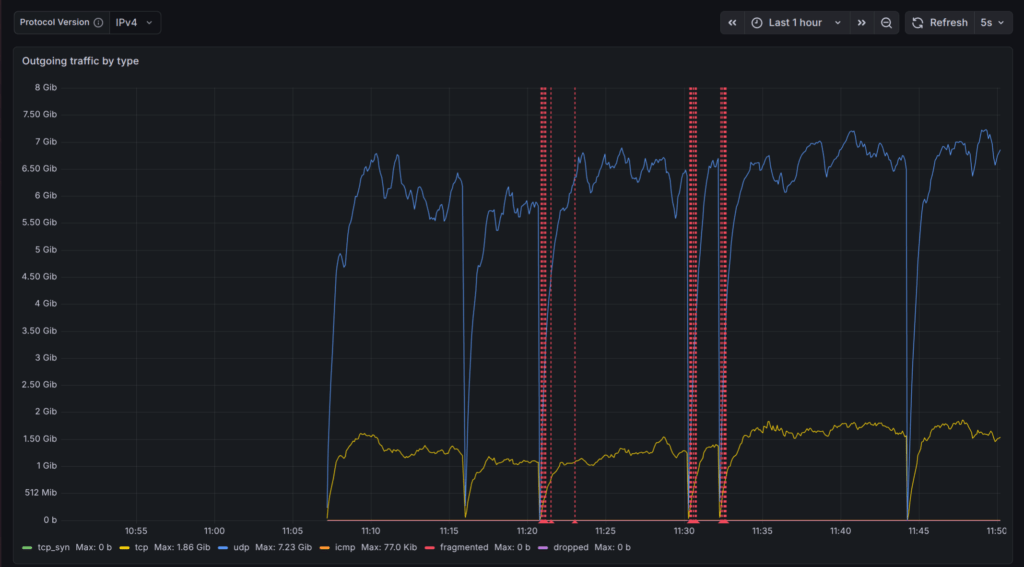
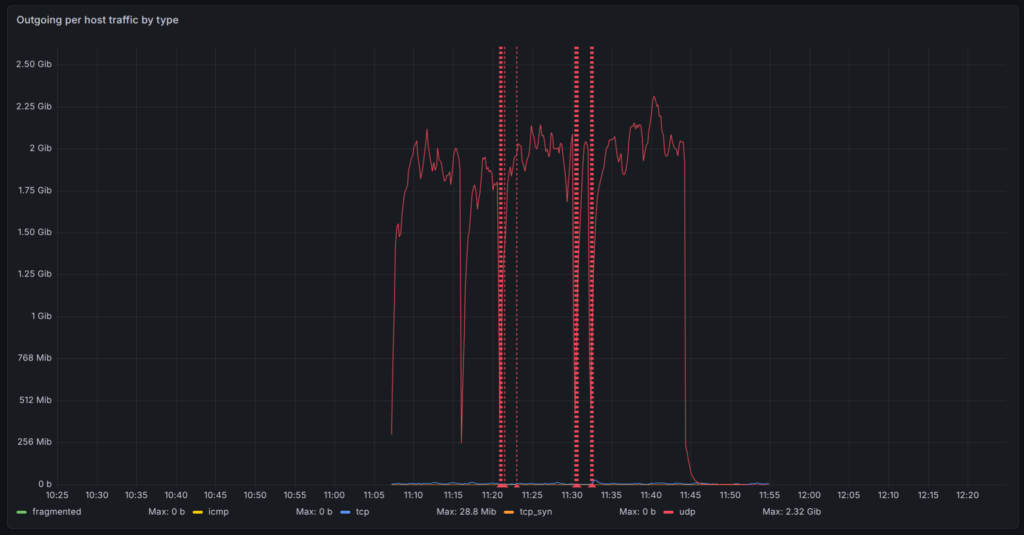
We are tracking a significant surge in outbound DDoS activity originating from residential broadband networks across India. Over the last 72 hours, traffic analysis indicates abnormal outbound UDP patterns affecting hundreds of networks.
This analysis is based on telemetry from a major Broadband Network Gateway (BNG) vendor and corroborated by several operator observations. The activity consists of sustained outbound traffic dominated by UDP packets with highly unusual behavioural characteristics.
Key Traffic Observations
- Outbound traffic volumes exceeding inbound traffic across residential networks
- Coordinated traffic bursts occurring simultaneously across large numbers of subscriber hosts
- A portion of malicious UDP traffic sourced from port 443 at unusually high rates
- A large and shifting set of destination IP addresses and ports
- Some traffic targeting internal ISP infrastructure rather than external internet hosts
Distinguishing Malicious UDP from QUIC
While some UDP/443 traffic is expected due to QUIC-based applications, these upload-heavy, synchronised patterns deviate sharply from normal user behaviour.
"These patterns are consistent with compromised edge devices generating coordinated outbound traffic," says Pavel Odintsov, Founder of FastNetMon. "In several cases, traffic appears to target infrastructure within ISP networks themselves, which could indicate an intention to destabilize broadband gateways and NAT systems."
Risks to ISP Infrastructure
Outbound DDoS occurs when compromised subscriber devices (CPEs/IoT) send attack traffic outward. At this scale, the traffic doesn't just impact external targets; it threatens the ISP’s own BNG and NAT capacity by saturating state tables and processing power.
Detection and Monitoring Recommendations
FastNetMon’s detection technology enables operators to identify outbound DDoS activity early through analysis of network traffic telemetry and threshold anomalies across subscriber networks. FastNetMon encourages broadband operators to monitor for sudden outbound UDP spikes, abnormal packet rates from port 443, traffic to port 0, and concentrated destination patterns.