Ubuntu users experienced widespread service disruptions last week after a sustained DDoS attack targeted infrastructure operated by Canonical, impacting critical systems, including package updates and security-related services.
According to public statements, the attack began on Thursday, May 1, with Canonical confirming that its “web infrastructure [was] under a sustained, cross-border attack.” The disruption affected multiple Ubuntu and Canonical web properties, as well as backend systems relied upon by users and developers.
Update failures and API disruption
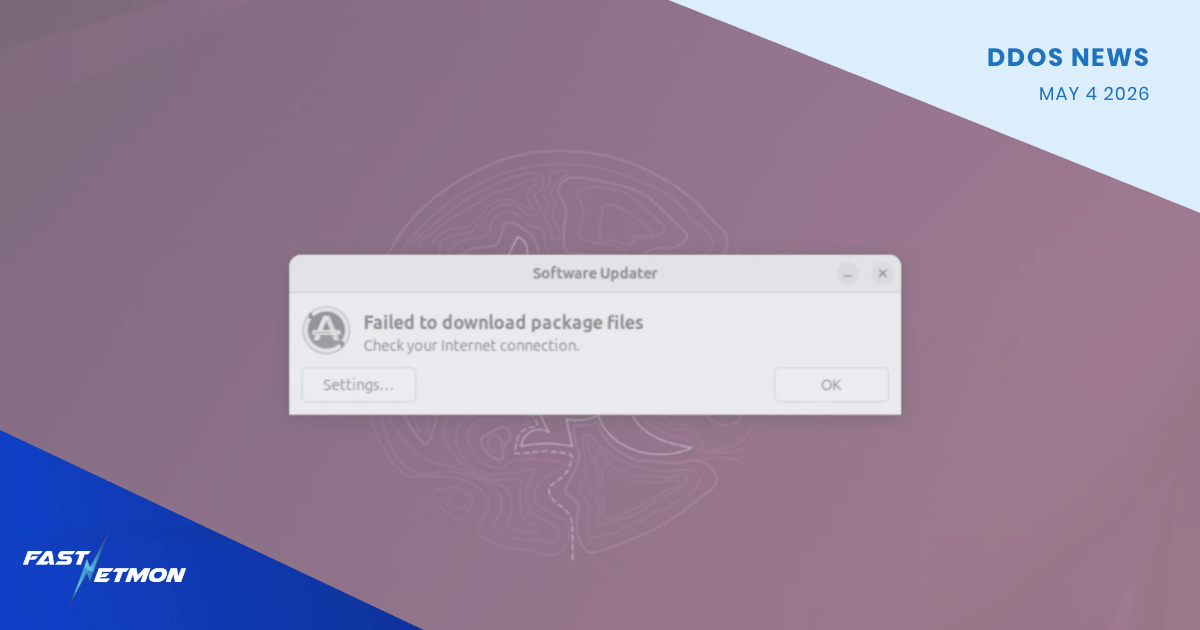
Reports from the Ubuntu community indicated that the attack impacted the Ubuntu security API and package distribution infrastructure. This had a direct operational impact: users were unable to install updates or retrieve packages from repositories. Independent verification confirmed that update processes failed on active Ubuntu systems during the incident window.
Given Ubuntu’s role as one of the most widely deployed Linux distributions globally, even short-lived disruptions to its update mechanisms can have cascading effects across enterprise environments, cloud workloads, and CI/CD pipelines.
Attack attribution and methods
A hacktivist group identifying itself as The Islamic Cyber Resistance in Iraq 313 Team claimed responsibility for the attack via Telegram. The group stated it leveraged a DDoS-for-hire platform known as Beamed.
Booter (or “stresser”) services like Beamed significantly lower the barrier to entry for launching large-scale DDoS attacks. These platforms offer on-demand traffic flooding capabilities, often advertising attack bandwidth in the multi-terabit-per-second range. In this case, the service reportedly supports attacks exceeding 3.5 Tbps.
Current status
As of today, Monday, May 4, all affected services appear to have recovered. According to Canonical Status Page, all systems are operational, indicating that Canonical has successfully mitigated the attack and restored service availability.