Distributed denial of service attacks (DDoS) are a significant risk to businesses of any size. One study found that recovering from a DDoS attack costs between $120,000 and $2m (£93,000 - £1.55m) depending on the size of the company affected.
Most of this cost is borne whilst fighting a flash attack and restoring services. Which means that identifying and blocking DDoS attacks can dramatically reduce IT security costs – particularly in relation to service disruption and breaches.
Speed is of the essence
Every organisation has mission-critical IT systems; any disruption or inability to access these resources will have a knock-on effect on operations. They must be available and operating optimally to maximise efficiency, productivity and customer experience.
A DDoS attack that affects access to key business systems will result in losing business to competitors. Worse still, lost customers may never return, particularly if the strike causes personal loss or damages the reputation of your organisation.
Consequently, DDoS attack detection and mitigation has to be fast and effective. Speed of response is crucial to limiting potential damage to network resources and the user experience.
It is also important to note that many DDoS attacks last less than 10 minutes. However, these ‘drive by’ incidents are typically just a test run, used by hackers as a proof of concept. Often they are a precursor to a more serious, sustained attack at some point in the future. Mitigating this initial attack will prevent re-targeting.
So-called ‘hacktivist’ groups rely heavily on DDoS attacks to cause widespread disruption - often for political reasons - to organisations across sectors including government, healthcare, education or finance. Often they are targeted for no other reason than their geographic location.
DDoS attacks are not just for cyberwarfare however. Sustained distributed denial of service attacks took popular games like The Last of Us and Grand Theft Auto offline for several days, potentially costing publishers Sony and Rockstar Games millions of dollars in lost revenue.
Accelerating response to DDoS attacks is therefore essential to protecting revenue and maintaining full operationality.
How FastNetMon accelerates DDoS response
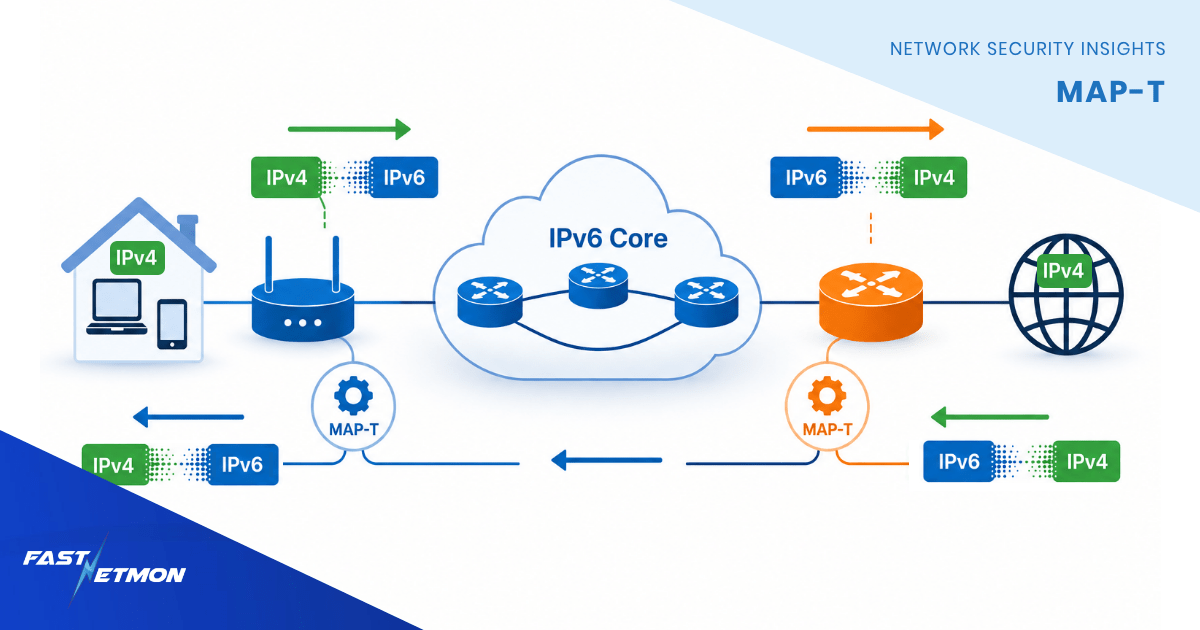
An effective response to DDoS flash attacks requires constant, in-depth monitoring. To assist with this process, FastNetMon uses state of the art traffic telemetry protocols available from some vendors.
There are two protocols which may help to improve attack detection speed and provide more information about attack vector:
- sFlow v5 from InMon Inc
- PSAMP based family of protocols as described in RFC 5476
sFlow is a well known protocol but it’s available mostly on switches and rarely can be found on routers which opens a large gap for deployment of rapid detection as the majority of Telco networks use routers to export traffic.
Recently multiple vendors such as Cisco and Juniper introduced support for new PSAMP based protocols. They use brand specific names such as Cisco IPFIX 315 and Juniper inline monitoring service.
These protocols are implemented on a data plane and do not use any aggregation which may delay export of traffic to DDoS sensors. In addition to that, these protocols provide raw packet headers which allow them to extract all the information available in the packet and identify malicious traffic with greater precision.
FastNetMon has solid support of these protocols and its high performance multi thread telemetry traffic information ingestion engine can handle telemetry from Terabit scale networks without any issues.
Note that these network telemetry protocols are available in:
- Juniper MX routers (inline monitoring services)
- Cisco ASR9000 and NCS 5500 routers (IPFIX 315)
You can find step-by-step configuration instructions for these devices here.
Why use PSAMP based telemetry protocols?
When enabled, PSAMP based monitoring allows FastNetMon to recognise an attack in just two seconds. This rapid detection allows for a rapid response – and provides an opportunity to mitigate an attack before web application performance is significantly affected.
This is important when you consider the average DDoS attack has gone from 30 minutes duration in 2021 to 3000 minutes (50 hours!) in 2022. Blocking an attack within two seconds offers major, long-term benefits, highlighting the importance of ultra-fast detection and response.
To learn more about FastNetMon and how we can help you with fast DDoS detection and mitigation, please get in touch.